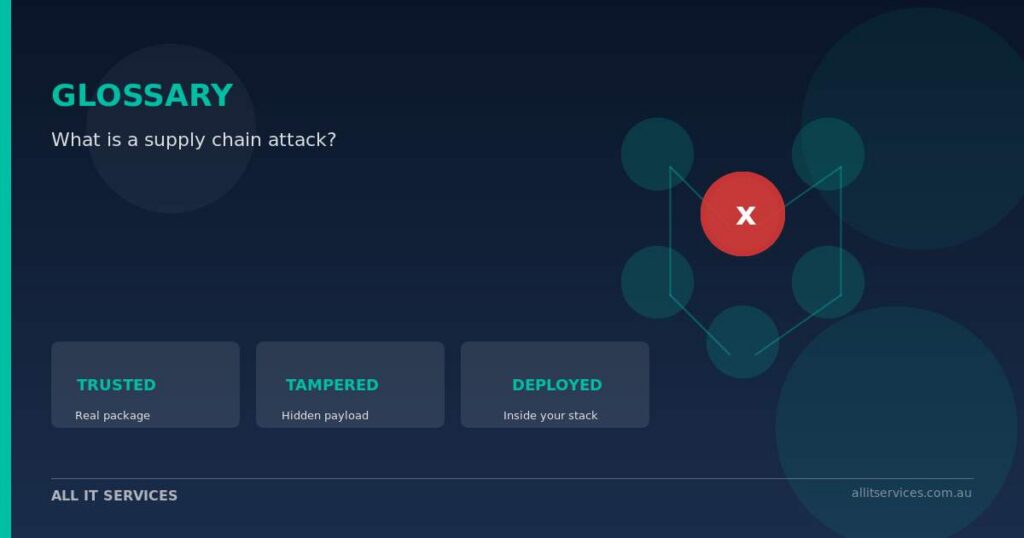
A supply chain attack is when an attacker quietly poisons a piece of software you already trust — a library, a tool, an update — so that when you install or update it, you also install their malware. You haven’t been hacked directly; the supplier has, and you inherit the breach. Last week’s compromise of PyTorch Lightning, a hugely popular Python AI training library, is the textbook example. As reported by The Hacker News, attackers pushed two booby-trapped versions (2.6.2 and 2.6.3) directly to PyPI on 30 April. Anyone who ran pip install lightning in those 42 minutes got a hidden payload that hunted for SSH keys, cloud credentials, GitHub tokens, and crypto wallets — according to Socket researchers.
If you don’t run an AI team, you might be tempted to scroll past this one. Don’t. The same pattern hits everyday business software: NPM packages behind your booking system, WordPress plugins on your website, MSP agents on your laptops, browser extensions on staff machines. The Australian Signals Directorate has been flagging exactly this trend — increased targeting of code repositories and tampered packages — in its current alerts. The Privacy Act doesn’t care whether your data leaked because you were careless or because a vendor’s vendor was compromised. The notification obligation lands on you either way.
Practical implications for an Australian SMB are simpler than they sound. Ask your IT provider three questions: which third-party tools and packages do our systems pull in automatically, who signs them off before they reach our environment, and how would we know if one was tampered with? If the answer to any of those is a shrug, that’s the gap to close. Pinning software to known-good versions, rotating API keys regularly, and reviewing browser extensions on staff laptops are all cheap controls that blunt this attack class.
If you’d like a second set of eyes on the supply chain risk in your environment, our cybersecurity team works with Australian SMBs on exactly this — vendor controls, software inventory, and incident response when a trusted package turns out not to be.
Related Guide
Cybersecurity for Sydney SMBs
Explore our complete guide to protecting your business from cyber threats.